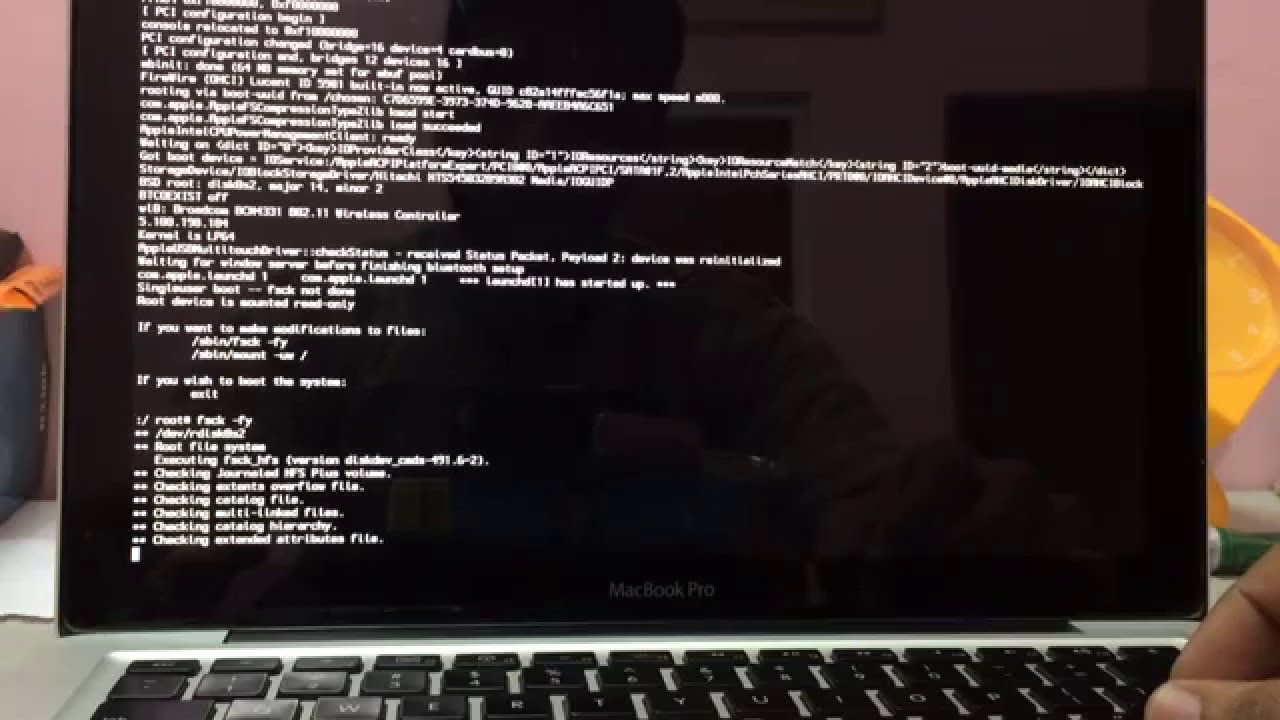
On macOS, go to Terminal and enter specific commands. You can find a tutorial here. If your webcam light turns on a few seconds after you reboot your computer, without launching any applications – you might’ve been hacked. If this is what’s happening, move on to the next step. Sep 16, 2019 Bluetooth Vulnerabilities Abound. At first glance, it might seem like it’s pretty risky to use Bluetooth. At the recent DEF CON 27 security conference, attendees were advised to disable Bluetooth on their devices while they were there. Of course, it makes sense you’d want to be more careful with your device security if you’re surrounded by thousands of hackers in a fairly small venue. Mar 08, 2013 Mac users get hacked, too. How to Increase Laptop Battery Life. This is an open-source AV engine that detects both Windows and Mac threats, and can be quickly fired up in.
Not a day goes by that we don’t hear about cybersecurity threats – be it data breaches, phishing scams, ransomware, and viruses – but what about protection against someone remotely accessing your webcam?
After all, Facebook founder Mark Zuckerberg and former FBI Director James Comey both put tape over their computer’s camera when not in use, so perhaps you should, too.
You don’t need to be a powerful person in the public eye to be concerned. In January, the U.S. government charged an Ohio man for 13 years of cyber theft , alleging he used malware to steal personal data from thousands of people, plus take over cameras and microphones that allowed him to 'to surreptitiously record images and audio.'
Aug 22, 2016 1 # Can I Tell If My Mac Has Been Hacked. To determine if your mac has been already hacked by hackers you have to know if things. First of all, you've to spot some sign of possible hacking. You'll have to consider whether anything out of the usual is happening on your notebook. You know how your computer runs better than anyone else. Apr 02, 2020 Mac. Open Finder or click the desktop. If you determine that your computer or smartphone has been hacked, there are a few things that you can do to prevent the. I’m going to answer the question you asked, then the question you might mean. The MAC address is the physical “serial number” of the network card in your device.
If you’re not sure what to do, the following are a few precautions you can take to minimize the odds of this happening.
Unplug or cover up
If you’re using an external webcam – that is, one that plugs into your computer’s USB port – only connect it when you need it. Yes, it can be a pain to remember to plug it in whenever you want to Skype or FaceTime with someone, but at least you’ll know 100% noone is spying if there’s no camera connected.
Mac Laptop Amazon
Some external cameras have a small cover you can close over the webcam lens, so be sure you take advantage of this when you’re not using it. If your webcam doesn’t have this, you can point it to the ceiling until you need it (but that doesn’t mute the microphone) or place a small piece of electrical tape on the front of the webcam. But don’t place it directly over the lens or else it could leave a sticky residue. You can also buy little stickers or covers to place over your laptop’s lens.
More: 5 security mistakes you're probably making
Macbook Air
More: A Website live streamed unsecured webcams like one at a daycare center
Use anti-malware software, good passwords
If your laptop or desktop has a built-in webcam, be sure to have good computer security software installed (which you should have anyway, of course). A strong security suite includes antivirus, anti-spyware, a firewall, and other tools to keep the bad guys from getting in. It’s critical to keep the security software up to date.
Many webcam hackers use Trojan horse malware to secretly install and run remote desktop software without your knowledge. You may think you’re downloading one thing, when in fact it’s carrying a hidden payload. Don’t click on attachments or any suspicious links in an email, text, or social media message.
Some web browsers also notify you if your webcam is being activated and you may be prompted to agree.
Be sure your wireless network has strong security settings and a good password – not the default one that came with the router — to prevent outsiders from accessing your Wi-Fi network without your consent. Resist using free, unsecured public Wi-Fi hotspots in cafés, hotels, and airports.
Another tip is to go to the webcam’s settings/options and enable some kind of notification when it’s being used, such as a small light that turns on near the webcam or a sound alert – if it doesn’t do it already. Most will have a small light illuminate when activated.
More: Virgin Media hack risk is a wake-up call to check your router

More: How to keep hackers out of your router
More: Hackers hid malware in CCleaner, a free app meant to clean out computers
Repair? Beware!
If you need to have your computer repaired, take it to a trustworthy source and then ensure remote access programs aren’t on your laptop or desktop you didn’t install yourself. If you find something, immediately uninstall it and bring it to a trusted source.
On a related note, be cautious about where you solicit remote tech support. Don’t let a technician take control over your computer to help you, unless you fully trust the source.
More: Web-connected medical devices are great. Unless...
More: Time to do a 15-minute cybersecurity makeover
Follow Marc on Twitter: @marc_saltzman. E-mail him at www.marcsaltzman.com.
It can be difficult to detect a hacker on a computer because the hacker will hide or disguise their actions. Below are the most common things that you may notice after a computer is hacked.
NoteIt is very difficult, if not impossible, to determine who hacked a computer or detect who is actively hacking a computer.
TipMost computer problems are not caused by computer hackers. It is more common for a computer to be hijacked by a virus than to be hacked.
New programs installed
In some situations, you may see new programs or files on the computer. If you are the only user on the computer and new programs are installed, this could be an indication that it was hacked. However, there are also several legitimate reasons why a new program may appear on the computer, as listed below.
- Operating system or other program received updates that included new programs or files.
- When you installed a new program, other programs may be installed with it. For example, it's common for plugins and other free programs to have a check box verifying the installation of a new toolbar or antivirus program. If you don't uncheck these boxes, the additional new programs are installed.
- If you suspect someone may have used your machine, ask if they installed a new program.
Below is a listing of programs that may indicate a hacker was on the computer.
- Backdoors and trojans are by far the most common programs installed on a computer after it is hacked. These programs can allow the hacker to gain access to a large amount of information stored on your computer.
- IRC clients are another common way for a hacker to get into a computer or remotely control thousands of computers. If you have never participated in an IRC chat and have an IRC client your computer may have been hacked.
- Spyware, rogue antivirus programs, and malware might be an indication of a hacker. More commonly, however, they are a sign that your computer was infected via download or visiting a hijacked page while on the Internet.
Computer passwords have changed
Online passwords
Sometimes, after an online account is hacked, the hacker changes the password to one or more accounts. Try using the forgot password feature to reset the password. If your e-mail address has changed or this feature does not work, contact the company who is providing the service. They are the only ones who can reset your account and give control back to you.
Local computer password
If your password to log into your computer has changed, it may have been hacked. There is no reason why a password would change on its own.
E-mail spam being sent
When an e-mail account is taken over, the attacker often uses that account to spread spam and viruses. If your friends, family, or coworkers are receiving advertising e-mail from you, your e-mail may be compromised. Log into your e-mail account and change your account password.
TipE-mail addresses can also be spoofed without hacking the account. After changing the e-mail password, if your friends continue to get e-mails you have not sent, it is likely someone is spoofing your e-mail address.
Increased network activity
For any attacker to take control of a computer, they must remotely connect to it. When someone is remotely connected to your computer, your Internet connection will be slower. Also, many times after the computer is hacked, it becomes a zombie to attack other computers.
Installing a bandwidth monitor program on the computer can help determine which programs are using bandwidth on your computer. Windows users can also use the netstat command to determine remote established network connections and open ports.

However, there are multiple legitimate reasons why your Internet connection may also be slow.
Unknown program requesting access
Computer security programs and firewalls help restrict access for security purposes. If the computer prompts for access to programs you do not know, rogue programs may be installed or it may have been hacked. If you do not know why a program needs access to the Internet, we recommend blocking access to that program. If you later discover these blocks cause problems, they can be removed.
TipA firewall prompting you for access may also be someone trying to probe your network, looking for open or available ports.
Security program uninstalled
If the computer's antivirus program, anti-malware program, or firewall was uninstalled or disabled, it can also be an indication of a hacked computer. A hacker may disable these programs to help hide any warnings that would appear while they are on your machine.
NoteIt is also possible for a virus to disable the antivirus program or malware to interfere with the anti-malware program.
Computer is doing things by itself
If your computer is deeply exploited, it's possible for a malicious third-party to remotely control your computer, executing any programs that you have privilege to run. If they are controlling your current login session, they can even control the computer as if they were sitting at your desk, using your keyboard and mouse.
For example, a mouse cursor could be moved or something could be typed. If you see the computer doing something as if someone else is in control, your system is likely being exploited at the root level.
Internet browser homepage changed or new toolbar
If you notice that your web browser configuration has suddenly changed, this may be a symptom of virus or malware infection. Examples of sudden browser changes include your homepage changing, a third-party toolbar being added, or your default search engine changing to something you don't want.